Cybersecurity is becoming more and more important in today’s world as technology advances and more sensitive information is stored online. One way to ensure the safety of your information is by performing a penetration test, also known as ethical hacking. If you’re new to the world of cybersecurity, the idea of penetration testing may seem overwhelming. However, it’s actually a …
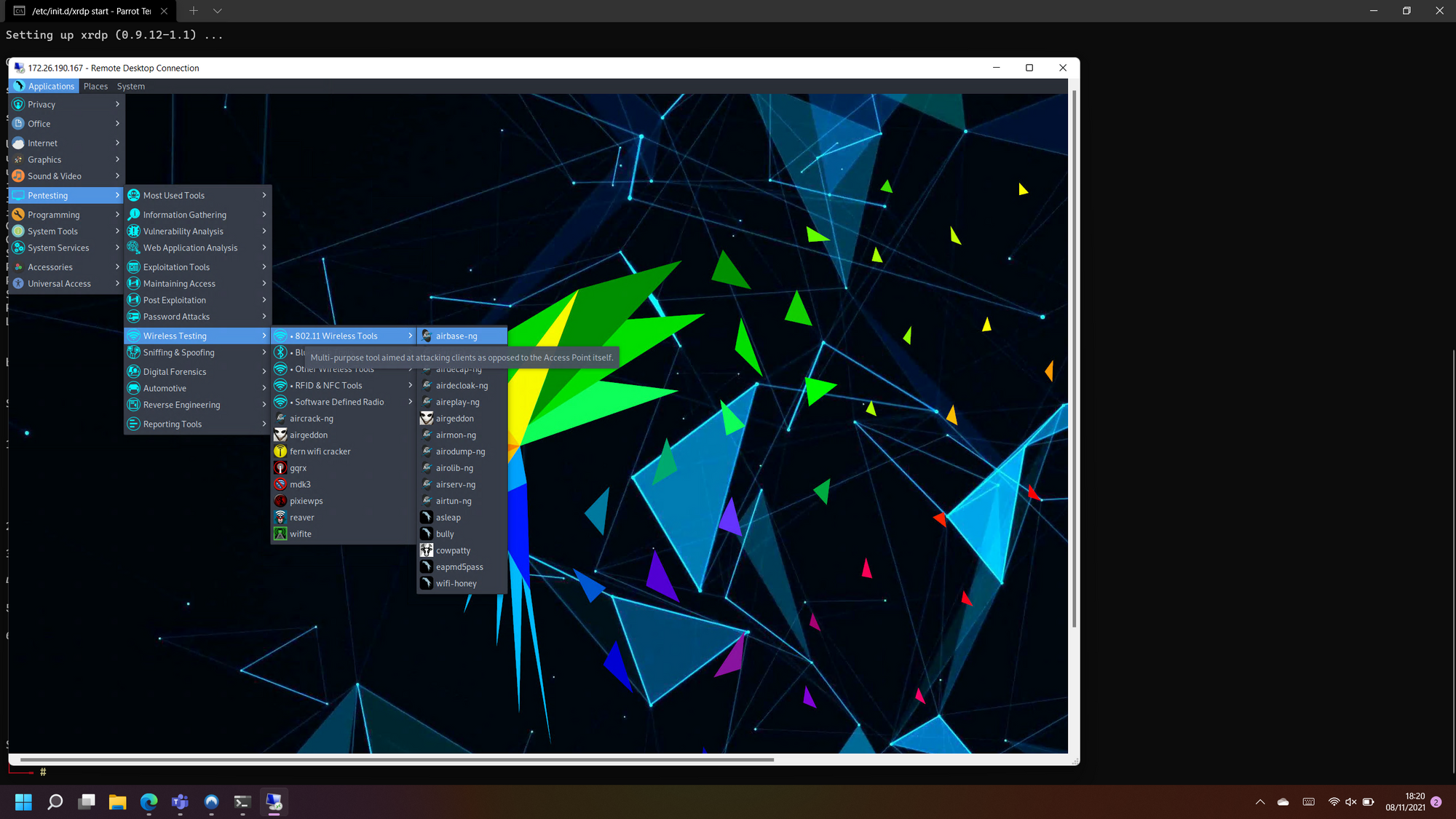
How to Run ParrotOS on WSL2
In this tutorial, I will show you how to get ParrotOS running directly on WSL2, running Windows 10 (ver. 2004 / Build 19041 or higher) OR Windows 11 x64. ParrotOS is very useful if you’re getting started in pen testing, as it already has all the useful tools installed that you need to get going. As with any pen testing …
Cybersecurity: Things to know going into 2022
Thanks to everyone who attended our tech chat today with Stetson, Lewis & Jason! It was great to see all of your cyber security questions coming in – sorry if we missed you! I hope it gave some valuable insight into the cyber security space in the near future, including your most vulnerable ‘Layer 8‘! We will definitely be doing …
WireGuard – VPN underdog?
Most of us have used a VPN for one reason or another. More recently, due to a heightened increase in “work from home” initiatives, companies have taken advantage of VPNs to keep employees ‘inside’ their networks, virtually. Not to mention the huge take up in VPN subscriptions for private use in recent years. For the most part, OpenVPN is the …
Whistleblower: Ubiquiti Breach “Catastrophic”
It has been reported that Ubiquiti have suffered a substantial breach of their systems. On the 11th January, Ubiquiti reported that a breach involving a third-party cloud provider exposed customer account credentials. A source who participated in the response to that breach alleges Ubiquiti massively downplayed a “catastrophic” incident to minimize the hit to its stock price, and that the …
Attackers place back door in Official PHP Git Repo
Attackers managed to implement a backdoor in PHP’s official Git repo. Two commits were made on Sunday 28th March 2021 which were apparent “minor adjustments”, however, enabled the ability to preform remote code execution on any server running PHP. This was shortly discovered by PHP users. Nikita Popov issued a statement, claiming “We don’t yet know howexactly this happened, but …
Ransomware everywhere! (And not a drop to drink…)
A High Level Guide to Ransomware OooooOooooOOoo, scary. Ransomware. You’ve heard about it, right? It’s in the name. “Ransom.” Indicating that something is being held hostage. But what? Your data. The answer is revealed below. Ransomware is a type of malware that encrypts data with an attached threat of perpetually blocking access or revealing secrets unless a ransom is paid. …
So, You wanna get into Cyber Security?
That’s great! But where to start? Cyber Security: The final frontier… Since there have been a few requests, here is a (short?) guide I whipped together in regards to starting out in Information Security. (Or, Cyber Security, whatever you want to call it.) The information here is applicable to many different positions, but best fits a security engineer, network security …