Since the beginning of the Internet, ads have been at the bane of it’s existence. From pop-ups, to pop-under, and everything in between, ads can not only hinder the end user’s overall experience, but in many cases, will completely turn a user away. As the Internet has evolved, so have the tactics of advertisers, embedding ads in virtually everything, including pre-installed software on smart phones; looking at you Samsung, Huawei, Xiaomi.
See also: active directory basics for it beginners.
These ads have grown from minor annoyances, to out of control entities that create both security and privacy concerns. Malvertising, a portmanteau of “malicious advertising, has become a vehicle for delivering malware via advertisements. Even one of the ugliest type of malware, ransomware, has been known be be spread via hacked legitimate advertisers. Needless to say, I believe pretty much everyone, outside those that work in advertising, have at minimal a distaste for ads, if not an outright hatred of them.
While ad browsing software for individual systems has been developed and in use for a few years, these companies, as companies tend to do, have been known for making deals with advertisers in order to let their ads “slip” through, many times splitting the profit from the ads displayed. And while less ads may be displayed, end users are still left at the whim of the ad blocking company who can also earn revenue from tracking users.
When 2014 rolled around, Jacob Salmela, decided to begin development on Pi-hole, an open source alternative to AdTrap. Originally developed to run on low cost Raspberry Pi single board computers, Pi-hole was developed using existing open source projects including cURL, lighttpd, and PHP, stitched together to deliver a lightweight, local area network, DNS and DHCP server which, by using pre-existing block lists, provided fast and reliable ad blocking for an entire network.
You might also find our 10 ai skills it pros need (56% salary boost) helpful.
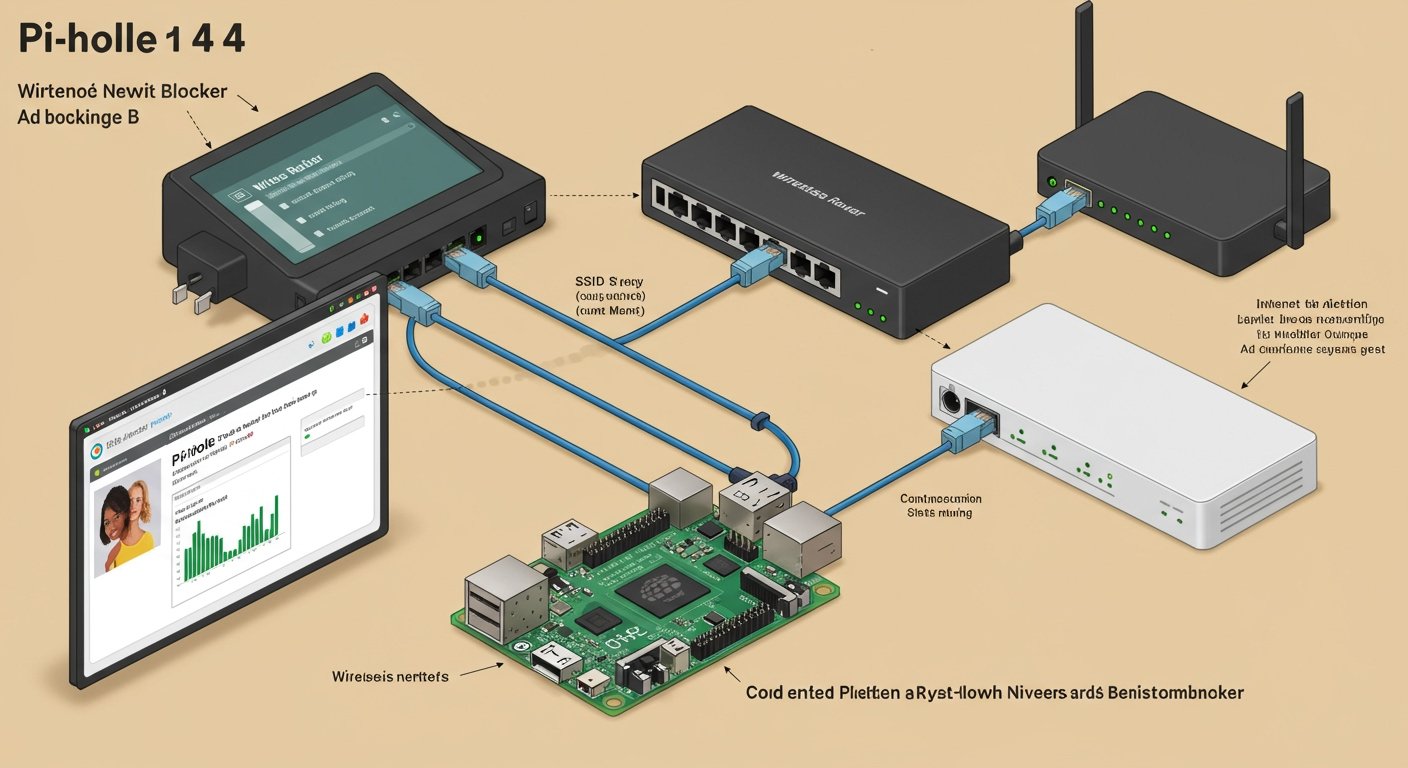
Here is a simple explanation of just how exactly Pi-hole works. Once installed and setup, Pi-hole will be set as the primary domain name server/system (DNS) on your network, via DHCP for dynamic addressing (either internal or through your router) or manually for statically addressed networks. Now when a user opens up their web browser of choice, every DNS request is routed through the Pi-hole. If the domain or host that the browser is requesting is in the block list for that Pi-hole, then the browser will be given the address of the Pi-hole instead of the actual IP address. As web pages are nothing more than a collection of files delivered from distinct hosts; static images can arrive via a CDN, HTML from the actual web server, and advertisement assets via scripts either served from or referencing known ad servers. Since Pi-hole will be delivering it’s local IP address (127.0.0.1), instead of the correct address for the items necessary to render and deliver the ads to your web page, the ad fails to deploy it’s payload onto your browser.
And here are the results:


Related: Learn about an it support group primer.


Pi-hole protects your entire local area network, including preventing ads from displaying in most mobile applications, as is the case with many “free” applications. Pi-hole also blocks tracking on most Smart TV devices, including those that collect and report literally everything you watch on those devices!
For more insights, check out our guide on ansible for it pros who hate repetitive work.
While advertising your Pi-hole as the LAN’s DNS, will work for most network connected devices, some manufacturers have decided to bypass any advertised DNS servers and use ones that have been hard coded into their firmware. While this does pose an issue, it can be easily by passed with a simple filter on your primary router. The basic premise is to add a rule to your router’s firewall to redirect all DNS queries originating from inside your network to be redirected to your Pi-hole’s IP address, as Chris demonstrates using iptables on his Netlink router running Tomato firmware. While this may differ from router to router, a simple google search of ‘redirect DNS to Pi-hole (ROUTER NAME)” should provide you with the exact steps to take to achieve this on your router.
Pi-hole is so lightweight and powerful, it can easily run on a $5 Raspberry Pi Zero, it can also run on practically any Linux distribution, including many NAS devices, like Synology, it can also be run from within a Docker container. That said, if you have more than just a handful of devices on your network, I personally would recommend running two instances, not only for completion’s sake in manual DNS entry forms, but also to provide some redundancy in case you have to reboot one device for upgrades or the like.
So if having a faster network, preventing advertisements, and creating an overall safer environment sounds good to you, head over to Pi-hole.net and get started today! Within minutes, you too can enjoy a much better Internet experience thanks to another open source project.
Once up and running, you’ll be presented with a fully fleshed out administration panel which will allows one to inspect a number of metrics to not only help you to understand your LAN’s traffic, but also troubleshoot hosts that may need to be added to the whitelist in order for some web sites to work (Some application, such as banking sites, require scripts loaded from ad server in order to work correctly; this is rare, but does remain true with a few of the larger banks). The administrative interface offers other tools including local host entries, whitelist/blacklist management, upstream DNS servers, DOH (DNS over HTTPS), authorization, API, etc. If interested, leave a comment, and I’ll write an entry regarding use of Pi-holes administrative interface.

If you truly enjoy this project, I would highly recommend becoming a Patreon supporter of the Pi-hole project.